Strengthening AWS Security with AWS Security Hub
The goal for this AWS Cloud Security focused lab was for me to use AWS Security Hub for centralized security monitoring.
AWS Security Hub aggregates security findings from different AWS services, allowing me to detect misconfigurations and threats in one place. As you can see here I enabled the CIS AWS Foundations Benchmark v1.4.0 which tracks 39 security controls:
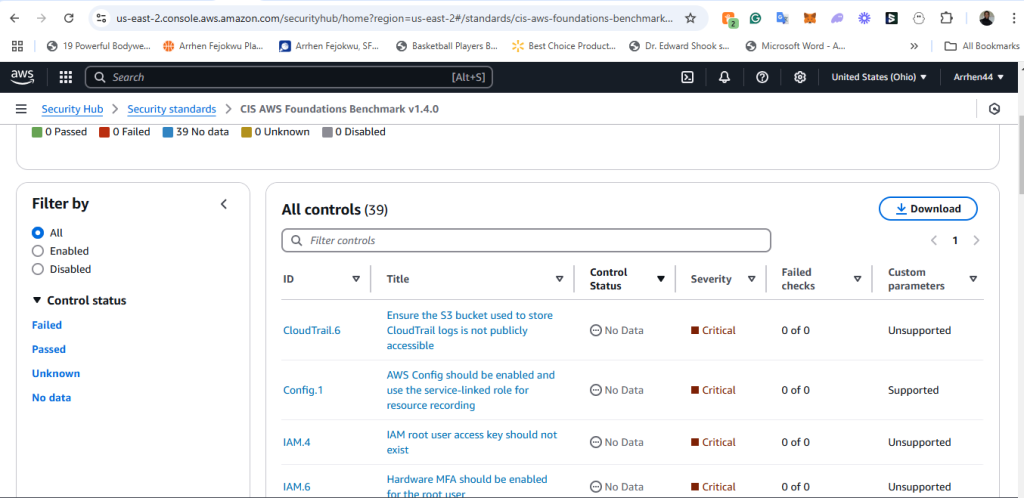
You can see in the screenshot above security controls like IAM.4, CloudTrail.6 and other controls are being monitored.
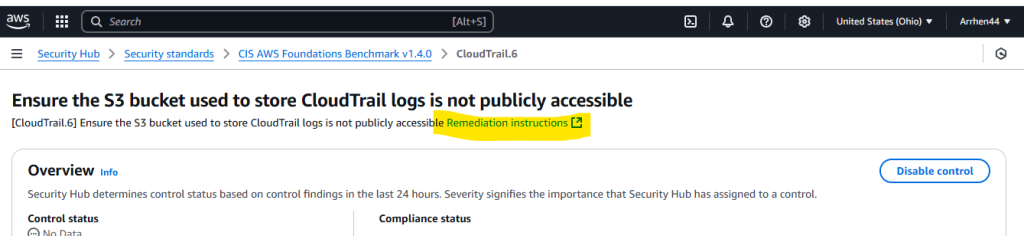
Next, I wanted to see if any findings where reported. I clicked on the control titled: Ensure the S3 bucket used to store CloudTrail logs is not publicly accessible.
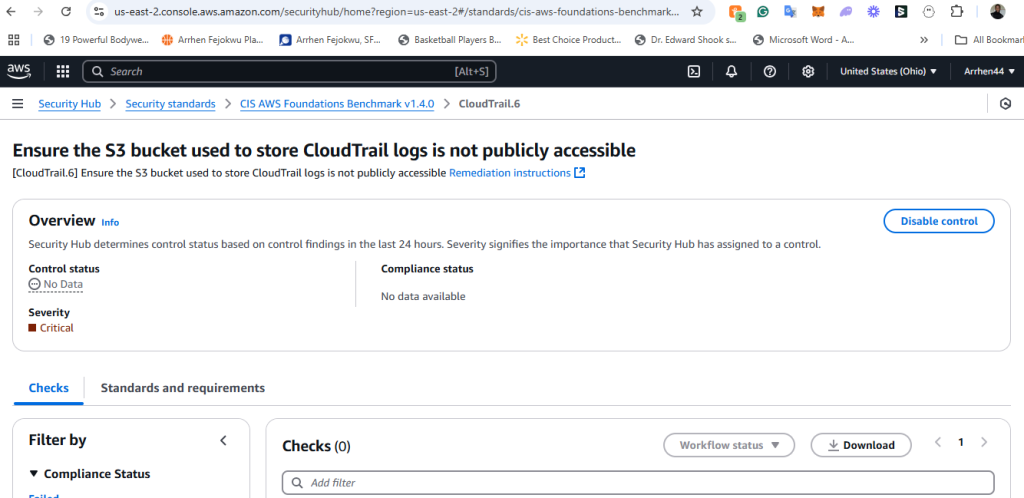
Finally, I was able to make a detemination that there were no findings to remdiate because no findings populated due to the simple fact that no checks were ran because there wasn’t any data to analyze . If a finding did show up, I would have quickly identified it and remdiated it as an exposed S3 bucket that could lead to a data leak and would be a critical security risk.
AWS provides remdiation instructions for each control which invaluable to a cloud security enginner.