Clawing Through Cyber: Unraveling the Meow Brute Force CTF Lab
This CTF lab was a an attempt and success to perform a simple brute force attack on a account that was left with a blank password.
Before starting the brute force attack I needed to ping the target’s IP address to see ensure my packets reach their destination. I ping’d the target here: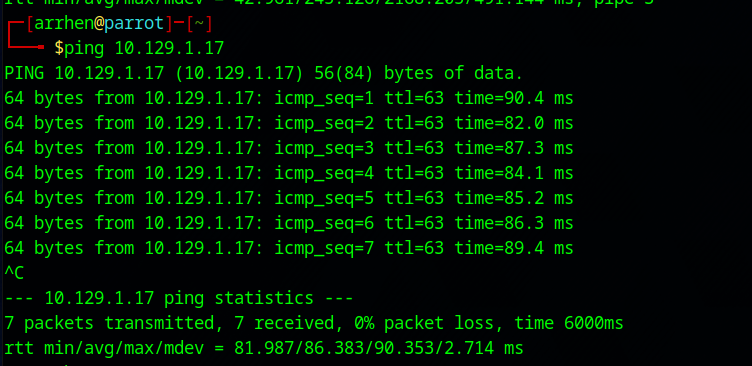
As we can see from the screenshot, 7 packets were successfully transmitted so we can determine that our connection has been formed and is stable.
Next, I started the scanning process using the
nmap & -sV script to send requests to target’s ports in hopes of receiving a reply, thus determining if the said port is open or not ,and since some ports are non-standard, I used the service detection flag -sV, to determine the name and description of the identified services as you can see below. 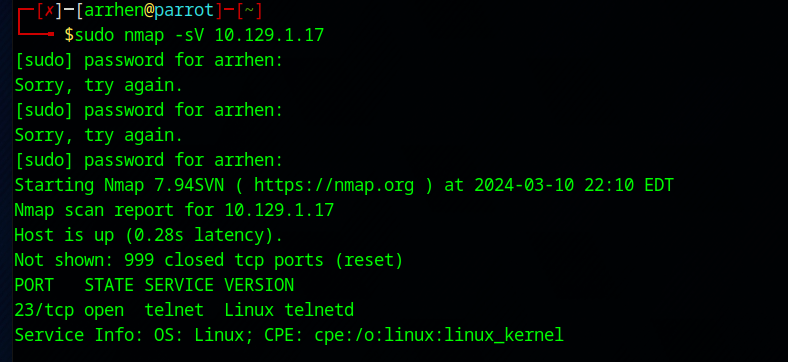
After running the scan I identified that port 23/tc is in an open state, running the telnet service. After a doinga quick search about what the telnet service is, I was able to discover that telnet is a old service used for remote management of other hosts on the network. Since connection requests through telnet are usually configured with username/password combinations for increased security. Sometimes, due to configuration mistakes, some important accounts can be left with blank passwords forthe sake of accessibility.I used this that knowledge to perform a simple brute force attack.
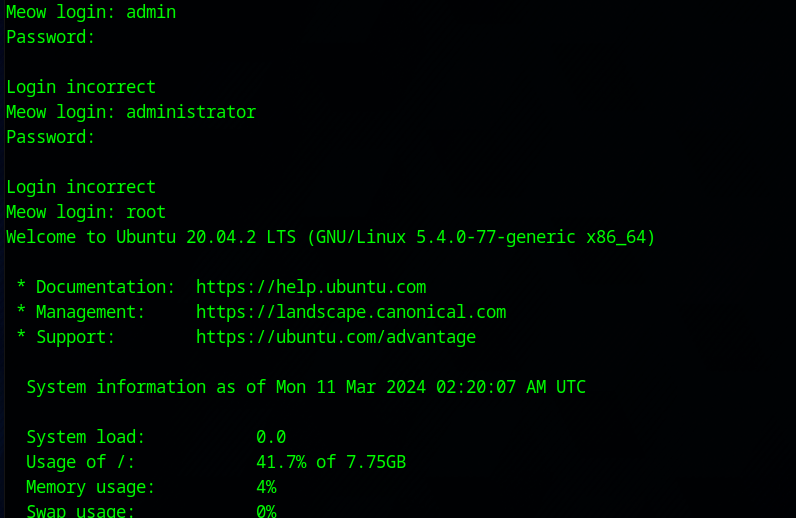
I manually inputted t these three basic usernames; admin, administrator, root. The last user name that I manually entered and a blank password worked I was able to login to the system successfully. After successfully login into the system, I knew I could use the LS command to find the flag.

I then knew that I needed to read the contents and have the hash value displayed of the flag.txt file so I used the the cat command. This give gave me the hash value of b40abdfe23665f766f9c61ecba8a4c19.