Using AWS Network Firewall to Protect Cloud Workloads
For this AWS Cloud Security activity, I am going to secure AWS VPC traffic with AWS Network Firewall.
To do that I need to first deploy the AWS Network Firewall into a VPC(Virtual Private Cloud). I deployed a AWS Network Firewall inside a AWS VPC which can be seen below:
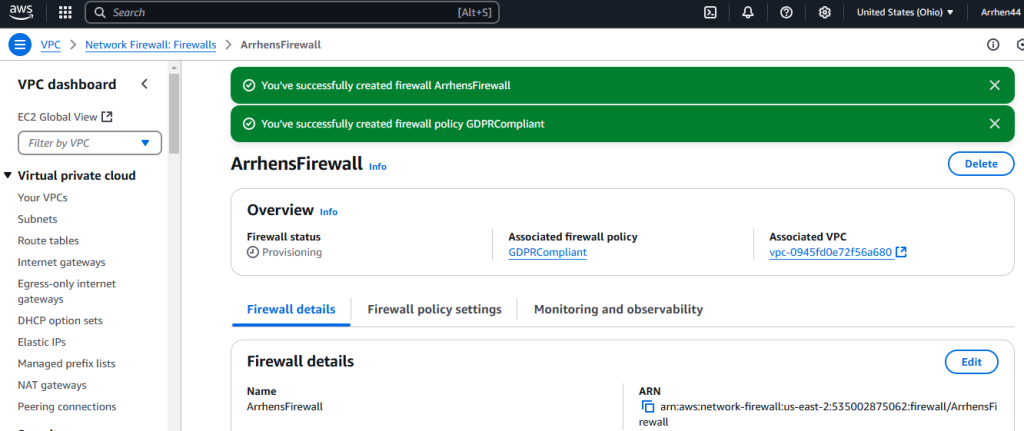
AWS Network Firewalls are important because AWS Network Firewall helps to prevent malicious traffic from reaching my AWS resources.
Next, I configured firewall rules. I configured rules to block unauthorized SSH access while allowing legitimate internal traffic The firewall rules settings can be seen in screenshot below:
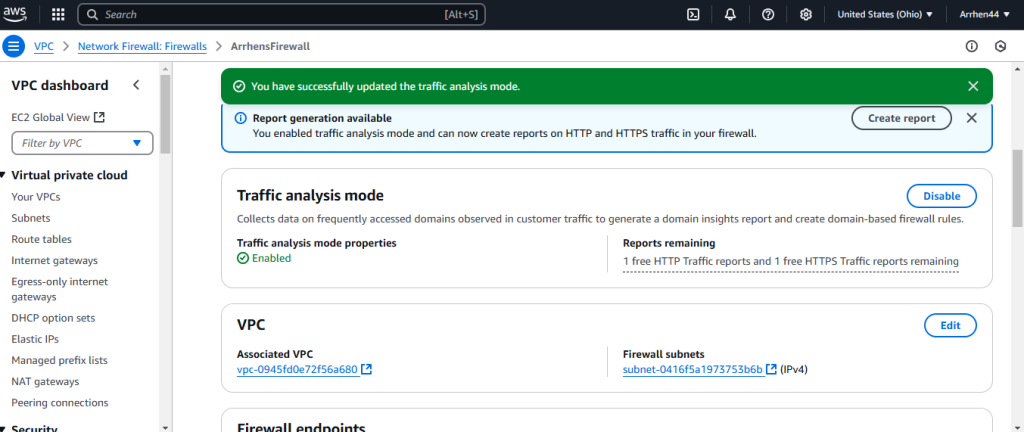
I started off by enabling traffic analaysis mode. Let’s say, hypotehtically speaking, the VPC was based out of the EU/Uunited Kingdom. I configured rules for a GDPR Firewall Policy to ensure this network firewall is compliant with GDPR. You can see an example of this highlighted in yellow below:
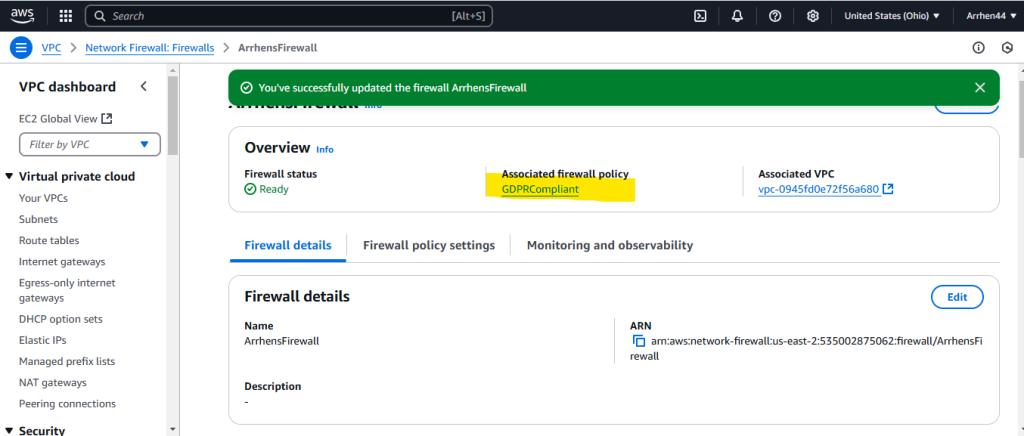
Next, I wanted to monitor any Firewall Logs for this firewall. The Network Firewall I created is called ArrhensFirewall.
I did this by navigating over to CloudWatch’s Log Insights to confirm that the firewall is successfully blocking unwanted traffic, and by doing so, protecting my AWS environment.
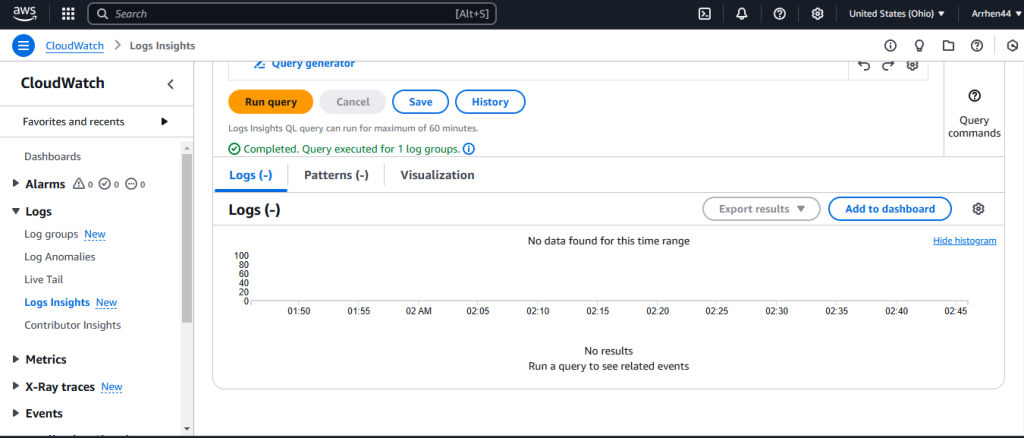
As you can see here in the screenshot the logs are empty becuase there there isnt any data to analyze, but when working correctly could show SSH attempts from untrusted IPs were successfully blocked, preventing unauthorized access.